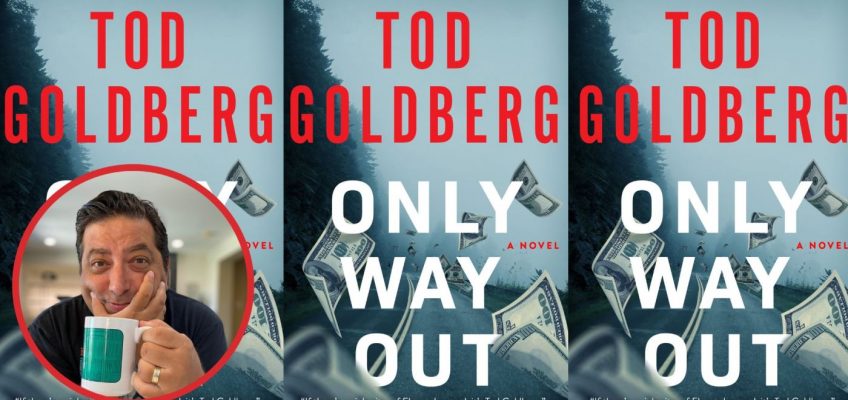
Tod Goldberg is the author of more than 15 books, including his Gangsterland series about a Chicago hitman who assumes a false identity as a Las Vegas rabbi. Goldberg’s latest is the crime novel, “Only Way Out,” about a crooked plot in an Oregon resort town that goes awry. As well as his writing, Goldberg founded and directs the Low Residency MFA program in Creative Writing & Writing for the Performing Arts at the University of California, Riverside. In a 2023 interview with this newspaper, Goldberg said, “In my books, there’s going to be a consequence. There’s always going to be a consequence for a bad thing someone does.” Here, he takes the Book Pages Q&A.
Q. Please tell readers about your new book, “Only Way Out.”
Like a lot of my work, it’s about bad people trying to be good, good people turned bad, and worse people caught in the middle. In this case, instead of being set primarily in the desert (though there is a section in the high desert…I can’t resist), it takes place in a dying resort town on the Oregon coast. And instead of Mafia gangsters, it involves smaller-time crooks, in this case a failed lawyer and his child-prodigy sister who plans an audacious heist, a crooked cop who stumbles on it, and an ex-con who knows too much. So, you know, a happy family story.
Q. What was it like doing a stand-alone novel after working for years on your Gangsterland books?
It was great fun. I’ve devoted the better part of the last 15 years writing about one character – Sal Cupertine, the Chicago gangster who hides out in Las Vegas as the Rabbi David Cohen – and while I enjoyed that immensely, I admit that I was getting restless to do other things. Some of that came out in my book “The Low Desert,” where I was able to expand the criminal universe I’ve been creating for most of my career in short stories, some of which took place in a version of the fictional town I’ve created for “Only Way Out.” On a craft level, it also meant I had to change the way I wrote, which was more challenging, since Sal/David’s voice is such a peculiar one that won’t work for all the stories I want to tell.
Q. Is there a book or books you always recommend to other readers?
I’m a real evangelist for Daniel Woodrell. His best-known book, “Winter’s Bone,” is a huge favorite of mine, but really his entire catalog is amazing.
Q. What are you reading now?
I just finished “The CIA Book Club: The Secret Mission to Win the Cold War with Forbidden Literature” by Charlie English, which has some, uhm, startling parallels to our present reality and then Susan Straight’s luminous new novel, “Sacrament.” She’s simply the best in the business.
Q. How do you decide what to read next?
It’s hard to say – I have a lot of books I haven’t read yet, and yet I keep buying more. Often, it’s the situation that I pick up something to “flip through it,” and then five hours later, I’m still sitting on the floor, my feet asleep, reading. I did just buy a signed Donald Westlake/Richard Stark novel from about 20 years ago – “Nobody Runs Forever” – and I’m planning on diving into that to justify that princely sum I paid for the late author’s work.
Q. Do you remember the first book that made an impact on you?
I do. “Of Mice and Men” by John Steinbeck. That book reordered my reality at ten years old. It’s the first time I recall crying while reading, and it’s the first time I experienced violence on the page that felt like an honorable thing.
Q. Is there a book or type of book you’re reluctant to read?
Well, I just can’t get through “Moby Dick.” I’ve tried. I have. It’s like how some people love tomatoes. I get it, they’re probably pretty good if you like them, but I don’t like the way they taste.
Q. Can you recall a book that felt like it was written with you in mind (or conversely, one that most definitely wasn’t)?
Oh, yes. “Get Shorty” by Elmore Leonard. When I read that book, I thought: Well, this is the perfect distillation of all my interests!
Q. Do you listen to audiobooks? If so, are there any titles or narrators you’d recommend?
I listen to more audiobooks these days than I read, which has mostly to do with my need to turn my brain off every night at bedtime. Audiobooks do a wonderful job of putting me into a meditative state. I just listened to “The Confidence Game” by Maria Konnikova, which I loved. And then it’s hard to beat Colin Firth reading Graham Greene’s “The End of the Affair,” which I highly recommend if you’re feeling like you’d enjoy a long car ride with a very depressed Colin Firth.
Q. Do you have a favorite book or books?
Of course. Too many, of course. But here’s a few: “Empire Falls” by Richard Russo. “Give Us a Kiss” by Daniel Woodrell. “The Laws of Evening” by Mary Yukari Waters. “Fifth Business” by Robertson Davies. “Mecca” by Susan Straight. “Columbine” by Dave Cullen. “The Devil in the White City” by Erik Larson. “Father’s Day” by Matthew Zapruder. “Trouble Boys” by Bob Mehr. “These Women” by Ivy Pochoda. “Out of Sight” by Elmore Leonard. “Your House Will Pay” by Steph Cha.
Q. Which books are you planning to read next?
“Subject: Punk: The Photographs of Maggie St. Thomas” by Maggie St. Thomas and “Crooks” by Lou Berney are queued up on my nightstand as we speak.
Q. Do you have a favorite character or quote from a book?
“I’m a detective and expecting me to run criminals down and then let them go free is like asking a dog to catch a rabbit and let it go. It can be done, all right, and sometimes it is done, but it’s not the natural thing.” – “The Maltese Falcon” by Dashiell Hammett
Authors and brothers Tod and Lee Goldberg each have books coming out in early September. (Photo by Hans Gutknecht, Los Angeles Daily News/SCNG)
Q. Is there a person who made an impact on your reading life — a teacher, a parent, a librarian or someone else?
My older brother Lee. He’s nine years older than me and when he left for college, he left me with bags of classic (and not so classic) crime novels, which essentially became my YA literature. This is why I probably knew more about hitmen than your average 6th grader.
Q. What do you find the most appealing in a book: the plot, the language, the cover, a recommendation? Do you have any examples?
I’ll follow an interesting character into any kind of fine mess. I’m fascinated by people who make very poor decisions, or people who are pushed into a corner, or people who are pushed into a corner and then make very poor decisions. I think of a book like “The Only Good Indians” by Stephen Graham Jones, one of the scariest damn books I’ve ever read, which I could not tear myself from, just to see what horrible terrible mess was to come next.
Q. Are you someone who must finish every book you start — or is it OK to put down the ones you don’t connect with?
I put books down all the time. This is why video games and streaming TV were created.
Q. Is there a book that tapped into an emotion you didn’t expect?
“Five Days at Memorial” by Sheri Fink and also “Ghettoside” by Jill Leovy. Both made me question preconceived notions I had about how society does and does not work.
Q. Do you have a favorite bookstore or bookstore experience?
My favorite bookstores’ experience of recent vintage came in 2016, the day after the election, when I found myself wandering the stacks at the late, great Sundance Books in Reno, NV, which was housed in this dying old mansion. I spent hours in the store that day, reading bits of books, going into and out of rooms, touching books, sitting quietly among printed friends, reminding myself that what we do as artists has a larger importance.